 Information sent over the Internet is at constant risk of being spied upon. Two Mount Allison researchers step into the shoes of online hackers to see just how secure this information really is. Dr. Liam Keliher from the department of mathematics and computer science specializes in cryptography, or how to protect information by using mathematical techniques so that spies can’t understand it. He and his student Karen Korstanje study the integrity of how information is protected, and they’ve found flaws in a new theoretical cryptography technique.
Information sent over the Internet is at constant risk of being spied upon. Two Mount Allison researchers step into the shoes of online hackers to see just how secure this information really is. Dr. Liam Keliher from the department of mathematics and computer science specializes in cryptography, or how to protect information by using mathematical techniques so that spies can’t understand it. He and his student Karen Korstanje study the integrity of how information is protected, and they’ve found flaws in a new theoretical cryptography technique.
“We often can’t prevent someone from seeing our information in transit,” said Keliher, “but we hope that we can put it into a form that makes it useless to someone [who wants to see it.]”
Most sensitive information sent online, from emails to the information entered in a web browser, is encrypted. This encryption is accomplished by two things: first, a cipher, or an algorithm which scrambles information in a way only someone who knows the cipher can unscramble. The second is the secret key used by the communicating parties. The key is of significance because the descriptions of most ciphers are freely available, so the key remains the crucial variable for fending off future attackers.
The academic study of cryptography falls into two main categories: creating these ciphers or finding their weaknesses. Keliher primarily studies ciphers created by other cryptographers to see whether they have any flaws, a discipline known as cryptanalysis.
“In order for something to be widely adopted, it needs not just to look good,” said Keliher, “but it has to be proven very rigorously that it can withstand all kinds of attacks that people will throw at because they will.”
Korstanje, a math and computer science joint honours student, spent last summer researching weaknesses in the Dhall-Pal cipher. The Dhall-Pal cipher was proposed in 2010 as a possible alternative to one of the most widely used ciphers for online information, the Advanced Encryption Standard (AES). This cipher is also used to protect information sent over Mount Allison’s wireless network.
“We developed a number of attacks. Our best one would let us get back the original message,” said Korstanje. She said this was possible by looking at the cipher’s secret keys, which modify how a cipher operates so that only someone who knew the secret key could decipher the message. Some of the Dhall-Pal cipher’s secret keys modified how the information was sent and in turn made it less secure.
While cryptography is based in theory, it usually involves computer coding.
“Algorithms are nice and beautiful and clean,” said Korstanje, “but it gets big and sprawling and messy [in code.]”
The academic discipline of cryptography is fairly new, originating in the 1970s with the popularization of personal computers.
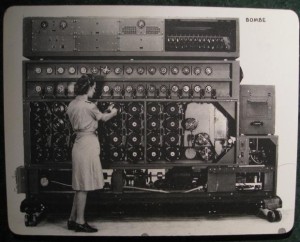
“Cryptography’s actually been around for thousands of years,” said Keliher. He and Korstanje said Julius Caesar used cryptography to send commands to his generals, while Alan Turing gained fame during World War II for breaking the Axis powers’ Enigma code.
Cryptography is considered a discipline of computer science but it involves more mathematics than some other computer sciences do. Korstanje said her expertise in linear algebra aided her research.
Both Keliher and Korstanje said job prospects are good for students with a background in cryptography.
“There are a lot of companies out there looking for people with an understanding in security protocols,” said Korstanje. “It’s definitely a field that’s lacking because its such a new field.”
Keliher teaches a class in cryptography every second year at Mount Allison. He said it was a fairly popular class and would like to teach it more often.





